What’s the true relationship between compliance and security? According to Evan Millman, compliance may not be security—but it’s the necessary starting point for building it. In this episode, Raj sits down with Evan to explore how organizations can shift their GRC approach from reactive checkbox checking to a proactive and risk-informed security practice. Evan shares stories from his work at Abnormal.AI, lessons from scaling GRC in fast-moving environments, and practical advice for anyone trying to align controls with business objectives.
5 Key Takeaways:
- Compliance is not the destination — but it is the framework for real security conversations.
- Say no to overkill — Right-size controls based on business needs, not frameworks.
- Decentralized GRC works — but only if there’s shared ownership and trust.
- “GRC therapy” is real — and it starts with building internal relationships.
- Metrics matter — but only when they tell a story that drives action.
What You’ll Learn:
- Why compliance ≠ security (but still matters)
- The pitfalls of checklist-first GRC programs
- How to build GRC partnerships across product and engineering teams
- Why business-aligned storytelling is the future of risk communication
- How Abnormal Security approaches frameworks like SOC 2 and ISO 27001
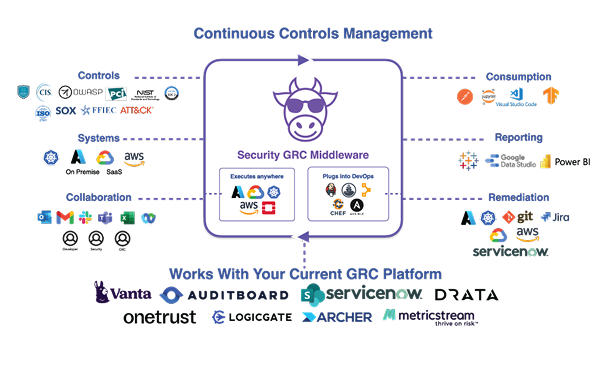
This podcast is brought to you by ComplianceCow — the smarter way to manage compliance. Automate evidence collection, eliminate screenshots, and scale your program with confidence. Learn more: compliancecow.com
Connect With Our Guest:
Evan Millman | Security GRC Manager | Abnormal AI
Connect on LinkedIn
Rate, review, and share if you enjoyed the show!
Subscribe to Security & GRC Decoded wherever you get your podcasts:
🕒 (Approximate) Timestamps
[00:02:40] What makes Evan passionate about security GRC?
[00:04:30] How compliance ≠ security — and why that distinction matters
[00:06:50] When GRC goes wrong: overkill, checklists, and inefficiency
[00:10:15] Building trust by embedding security into product discussions
[00:14:40] Right-sizing controls: starting with SOC 2 vs ISO 27001
[00:18:10] Managing a decentralized GRC team at Abnormal
[00:23:02] Metrics and storytelling — what the board actually wants
[00:29:45] Why GRC leaders need emotional intelligence and empathy
[00:35:20] What GRC professionals can learn from product managers
[00:39:11] Evan’s advice to vendors trying to break into GRC
[00:41:05] How GRC can (and should) enable product velocity
[00:44:55] If he could wave a magic wand, what would Evan fix in GRC?
Raj Krishnamurthy (00:01.173)
Hey, hey, hey, welcome to Security and GRC Decoded. I’m your host, Raj Krishnamurthy. Today we have the fantastic Evan Millman with us. Evan is a manager in abnormal AI. Abnormal AI deals with analyzing abnormal behavior signals and protecting against email phishing attacks and breaches. He has a very, very interesting background. From a political science student, isn’t that right, Evan? From a political science student to a network engineer.
to a GRC practitioner, an amazing and transformative journey. He’s here to talk about all of that and his fresh perspectives on what GRC is. Evan, welcome to the show.
Evan Millman (00:40.142)
Thanks for having me, Raj. It’s a pleasure to be here.
Raj Krishnamurthy (00:42.881)
So Evan, let’s start off with something very interesting. What is one heart take, one controversial opinion that you have of security or GRC and GRC?
Evan Millman (00:53.374)
sure. So I guess my first controversial opinion would be, and I don’t think maybe this isn’t too controversial because I’m sure plenty of people share this, but compliance does not equal security. and I say that as somebody who’s a GRC professional, just because you can pass an audit doesn’t actually mean that a control is preventing risk to an organization, right?
a lot of these frameworks that we all kind of, audit against or report against, they’re really more foundational. And, know, I understand why a lot of organizations view them as like the ultimate goal, but they really are not the ultimate goal. They’re really just like the start. They’re really just the foundation for building a practical, risk adverse cyber program.
So I think, know, organization, my hot take would be, know, organizations who put too much pressure on achieving, you know, whether that’s an ISO certification, NIST, you know, getting your SOC 2 report, putting too much pressure on that, I think, takes your eyes off the prize of truly creating a secure, risk adverse environment.
Raj Krishnamurthy (02:17.301)
But then why do people do it?
Evan Millman (02:20.43)
So first off, I would say people do it for two reasons. A, you still need something, right? Like you still need a way for a prospective vendor or a prospective partner or a prospective acquisition partner to assess how your internal policies, procedures.
your internal security program is functioning, right? So you still need a way to measure it. So that’s like one area where I do feel like these certifications and these reports do provide value because like you need something to measure. And then also from customers too, right? So like a lot of times, you know, it’s hard for a prospect of a customer to
really know how well your internal security program is made up, how well you are developing code, how well you are locking down access to certain systems or preventing data from being exfiltrated from your environment. So you need a way to kind of like prove that you’re doing something.
Right? And like the best way to prove to do something probably ends up in these type of reports. But again, I think people who really are really in tuned in the industry know that these reports are just the starting point.
Raj Krishnamurthy (03:59.074)
So I heard two things that you said, which is interesting. One, you said measurement. The other one is advertisement. mean, way I mean to say it, advertising the measurements. And you also said that people take this with a grain of salt, is what I heard. People understand the complexities and the constraints. So to what extent can you believe in these measurements? You deal with vendors in your role in abnormal security, and you also deal with customers.
So how do you view these measurements from vendors?
Evan Millman (04:32.142)
Yeah, great question. So I think a lot of that comes down to and kind of something that we practice that abnormal. For example, if you take like our third party risk management program, you know, just seeing that perspective, you know, vendor that we might want to work with has a SOC 2 report or their ISO 27,001 certified or 27,701 certified or what have you. Just seeing that as a checkbox.
is not enough. You actually need to read that SOC 2 report. Like read if there’s any report around the ISO certifications, actually dig into the details. Like what was in scope, what was out of scope is the product that you’re trying to buy is a provisioned in an environment that’s not even in scope in their ISO report. So actually getting into the details and not just viewing like
yeah, they have, you know, they’re ISO certified or they have a SOC 2 report. Like that’s not enough. Like you actually have to do more due diligence to go into the weeds to figure out what is that report actually reporting on? What is it actually telling me? And you know, having knowledge and experience of security in general should put you in a better place of say, okay, yeah, you might have, you know,
you might have your clean sock to report, but the product that I want to buy from you, that infrastructure is completely scoped out. So like how did that, that doesn’t, that sock report is now basically meaningless to me, or maybe there was a, a, a finding around, you know, access controls or DLP, you know, how is that then going to relate to, you know, the, the risk that that
that bringing that potential vendor onto your organization might present, right? So it’s more about like, it’s not, you know, taking these things with a grain of salt, but going, diving more into the details, you know, not just having it as a checkbox of like, okay, yeah, you have a certification, like, you know, we’re good here, like, no, like, what does that actually certification mean to that organization?
Raj Krishnamurthy (06:54.818)
And by that, do you go back and forth with the vendor and how much time do you spend if so?
Evan Millman (07:00.13)
Yeah, I mean, it’s hard, right? So like, there’s a constant pull. you know, Raj, you know, I’ve spoken about this before, like, I’m not somebody who will sit here and like pound my chest and say, security knows everything and we should stop whatever we’re doing for security. Like, at the end of the day, like, I work for an organization, a company, and we’re not a non-for-profit, right? We’re trying to sell a valuable product to a market.
and ultimately make money. So there’s always going to be a poll with security best practices and what’s in the best interest for an organization for a slew of other reasons, right? So you have to try, right? Like I always say to my team, like our job is not to fix anything. Our job is to use our knowledge and experience.
to find where there are flaws, where there are risks, where there are vulnerabilities, properly document them, properly understand them, and report that to the people that need to make this more complex business decisions. Our job is really to present the people, the business leaders, with our perspective. It’s not to make decisions, it’s not to…
change things while, know, caveat, of course, GRC and security can be a conduit to change things. But our job is really more to observe, report and advise.
Raj Krishnamurthy (08:40.865)
So you’re saying GRC is an observability layer for security and engineering operations.
Evan Millman (08:46.368)
Absolutely, absolutely. That’s how I view it. Yeah, 100%. Like, know, it’s not ultimately, you know, I can again, back to, you know, third party risk management, we, there might be some tool that our engineering team might want to start to use that will exponentially speed up the way in which we can deliver code to like the production environment. You know, my, you know, my team might get that vendor and do an analysis and say, well, it’s like,
It’s open source software and they’re really new and they don’t really patch their vulnerabilities. there’s a lot of risk here. But we might have told customers or the industry at large, like, we are going to be delivering these next three new features to our product by September.
And there might be a decision that has to be made of like, okay, well, if this tool is going to help us reach that business goal, is it, is it worth to stop everything and not proceed because security found some type of risk or is the business decision going to be made of like, Hey, noted, let’s, let’s not forget about this. Let’s figure out a way to remediate that or
decrease that risk with some type of compensated control or some type of contract language, but ultimately we’re going to procure this tool. We’re going to use this tool. like ultimately, we shouldn’t stop business from doing the things that it needs to do, but we should be a partner to help and make sure that we are making informed business decisions is guess how.
Raj Krishnamurthy (10:39.781)
That’s a great point. And this third party risk management toil that you’re talking about with your vendors, how does that influence how you deal with your customers?
Evan Millman (10:50.69)
Yeah, I mean, a lot. like, you know how we it’s kind of like you want to practice what you preach, right? So when we are so strict or raise red flags, because, you know, we find some prospective vendor that we want to use, they don’t enforce, you know, MFA, or they’re not using a
You know, it’s reported that they’re not using a password manager or they’re not using, you know, TLS 1.3 at this point. You know, it’s, it’s hypocritical, right? If we were to call something out on a vendor that we want to use and say, Hey, that’s too big of a risk that we don’t want to use it. But if we’re not, you know, doing those things ourselves,
It’s like, kind of leaves us in like that almost like, again, like a hypocritical type of state of like, well,
Raj Krishnamurthy (11:55.682)
I was going to say that I was barely, I was trying to contain but you’re absolutely right. Hippocritical is the right term to use I guess.
Evan Millman (12:03.276)
Yeah, exactly. you know, like we, you know, and again, but that goes back to business decisions, right? So like, again, us as GRC professionals, as security professionals, our job is to observe, report, get that information into the business owners. But at the same time, like that also should be how we drive certain initiatives internally. Like, hey, like if we’re concerned about
our vendors not using the latest level of encryption, shouldn’t we make sure that we ourselves are using the latest level of encryption? It’s like you can’t, you don’t have a leg to stand on. You’re not being truthful, you’re not being honest if you’re gonna tell somebody that like, hey, I don’t like what you’re doing, but I’m not doing that myself for whatever reason. If you’re not doing that yourself, that’s fine. But then how my team…
would view that type of risk should obviously be decreased, right? Like it should be at a level of like, okay, sure, that’s something of concern for us. But since considering that we don’t do that ourselves, we can’t, we don’t really have a leg to stand on to like force somebody else to do it.
Raj Krishnamurthy (13:17.643)
Makes sense, makes sense. I think you touched on a very interesting point. GRC has an observability layer to security and engineering operations. The fundamental question is that the cadences with which these teams operate, for example, you’re technology-first company, you’re a cloud-native company, you operate on Uber and Rapid scale, you’re making thousands of releases per week, Versus your assessment comes very less frequent.
once a once a year, how do you match these scalences?
Evan Millman (13:53.123)
Yeah, that’s a huge challenge, right? Actually, you know, I think it’s kind of something that I think is in the ethos of compliance cow of like getting to a state where audits are not a point in time type of thing that it’s constantly occurring all the time. And that’s something that we’re trying to work on internally at abnormal is
You know, the foundation of that is making control owners know and own, their own controls, right? Like security is really everybody’s responsibility. just like practicing good business ethics, just like practicing good, like accounting, you know, ethics, like security is everybody’s responsibility. It’s not just the security team. It’s not just the GRC team.
And the more that you can instill that culture foundationally into a company that everybody’s responsible here in some way to that, think that kind of like pushes the button a little bit to hit that, know, cadence where like, Hey, like we’re continuing to push you, like you said, thousands of releases, like in a short period of time. But Hey, we’re only auditing.
once, twice a year. Like, so how do you square that? You square that by like making the engineering teams feel more responsible for controls. And then honestly, you know, and we’ve kind of, we’ve, we’ve touched on this before where, you know, you know, I love my highway analogy, right? Like my car can go a lot faster than the 65 mile per hour speed limit that’s on a highway, but that
But there’s a reason that there’s a speed limit on a highway because of years of research and data.
Evan Millman (15:55.875)
governments figured out that it’s a safety issue, that if you do not go, if you do not exceed a certain threshold in your speed, the percentage risk of an accident happening decreases. So if you think about that in terms of technology and security, maybe we don’t have to push, you know,
so many updates as quickly as possible. Maybe there is a little bit of resetting expectations. This constant need to put your pedal to the metal as like the expression goes. Maybe loses sight of some security best practices and I think that there’s probably a happy medium there.
Raj Krishnamurthy (16:43.381)
Got it, got it. So you’re saying that there has to be a balance between how quickly we push and obviously consequently break versus how secure we are. But you’re not advocating that you stop. You’re not advocating at the cost of innovation. You’re advocating at the right balance.
Evan Millman (17:02.006)
Absolutely not. I hate traffic just like anybody else, right? To go back to my analogy, right? Like, 100 % you shouldn’t stop and frankly, you know, we’ve all been on a road where the speed limit doesn’t make sense, right? Or it’s super late at night and there’s nobody on the road and like, okay, if I go 75 or if I’m touching 80 here, like no harm, no foul kind of thing. So like there is always…
Raj Krishnamurthy (17:04.117)
Ha ha ha.
Evan Millman (17:31.691)
expect, you know, exceptions. There’s always ways to cut out. yeah, absolutely not. Again, it goes back to like, I’m somebody who believes like, that ultimately the business purpose is what’s going to drive decisions, right? It ultimately, it’s a business decision. It’s not a security decision. Everything is a business decision. And yeah, maybe for a company pushing code out
very fast in a short amount of time. Maybe that is in the business’s best interest. But then I would argue then you need to have a robust compensating control to make sure you’re not just completely forgetting about security. Because what happens is you just accumulate a ton of tech debt, right? So like then all of a sudden one day you want to take patching vulnerability seriously and you just have a backlog.
that’s almost like unworkable, right? It’s just like where you even begin. And then you wanna sign, and then your company picks up speed and you wanna sign bigger and bigger, customers and they’re gonna start requiring that you have all your criticals patched within 72 hours kind of thing. And you’re almost like you’re…
Speed sometimes takes your eye off the site of there are other factors in play here, right? So like if you do need to kind of push code out to production in an expedited manner, you got to make sure that you’re accounting for that in some manner.
Raj Krishnamurthy (19:18.315)
Got it. And you said that when we talked about the cadence, you said that you want to see the control owners being more accountable. If I’m the engineer sitting in building the product, right, or even in security engineering, I am on a go, go, go basis, right? mean, this may sound blunt, but I care the least about compliance for governance or risk in some ways. How do you…
Evan Millman (19:45.07)
100%.
Raj Krishnamurthy (19:48.033)
build that cultural change, how do you bring that cultural change so that they do care?
Evan Millman (19:55.023)
It starts from the top down, right? Like it has to be. It has to be senior leaders, your CTO, your CIO, your CISO. They have to make it your responsibility. They have to make you want to care, right? Like I’ve never worked on an engineering team. It’s outside of my level of comfort, but how they are evaluated, how your personal
performance review is evaluated from a engineering perspective is obviously in a way could it be a lot more quantitative than maybe somebody like on my team, which is a little bit more qualitative, right? Because we’re working on like on projects and procedures and policies and like, there’s not a lot of like, okay, how many lines of code did you push like to production? Like there’s actually like tangible quantitative things that you can actually measure.
on an engineer to measure performance. Like I would argue that from the top down, some measure should be also like how secure is your code? did you, how many times did you stray away from like our SS DLC? How many times did you push code to production that might have had some type of vulnerability in it? Listen, of course, sometimes you don’t know, right? These things you can push code to production and think everything.
is kosher and clean, but six months down the line, there’s some new exploit that’s found that you just don’t know about. Of course that’s going to happen. But just instilling that culture that, again, that everybody is responsible. They’re like, yes, I get it as an engineer. All you care about is closing out your Giro ticket and making sure that you’ve fulfilled the requirement.
Raj Krishnamurthy (21:46.261)
You
Evan Millman (21:51.949)
you know, through whatever code that you needed to edit or create new. But like, I would also argue that if you really have a security minded culture at an organization, part of that is also, I doing everything possible that before I push code to production, that it, as per today’s standards right now, it is that that is as secure as it possibly can be.
Raj Krishnamurthy (22:20.113)
And what do see is the role of GRC teams in those measurements, those measuring those drifts?
Evan Millman (22:27.758)
Yeah, so again, it’s kind of that like observer and auditor, right? Like I want to say like in a way, GRC team is kind of like the referees, right? You know, out there. where we should be observing the game that’s going on or the, you know, the work that’s being done and reporting on where we see issues or where we don’t see, you know, or, or, or,
vulnerabilities that pop up and working to remediate that, right? But again, it’s not working in a matter of let’s drop everything because I found these three critical vulnerabilities and stop pushing code to production because we need to fix these first. It’s more, okay, we noticed, you know, we, we observed these risks. Who do we need to talk to, to address these? How do we get these addressed as soon as possible?
without disrupting our overall business goals.
Raj Krishnamurthy (23:34.281)
And Evan, how do you see governance, risk and compliance and the dependencies between them and the interplay with security?
Evan Millman (23:43.727)
Sure, I mean governance is kind of like what we alluded to just now, like is us being that like that traffic cop, that referee to kind of like make sure that teams, whether that’s your accounting team or your people ops team or your engineering teams are adhering to security best practices, our own internal policies and procedures, right? So like that’s like the governance aspect of it.
the risk aspect of it is when we find somebody or some team or some process that strays away from either our internal policies and procedures or security best practice. Our job then would be to observe that record that, figure out a way to remediate that and work with the appropriate stakeholders to
Ultimately, you know to to to close out that gap then the compliance comes in from kind of You know a combination of ensuring that we’re adhering to policies and procedures and then you know just very bluntly like Making sure that we’re aligned with our whatever standards that you know the organization, you know, for example, you know, um You know we go for ISO 27,001 like making sure
that there is nothing that’s being done at the organization that would potentially cause us to have some type of finding from an audit. like observing and being that traffic cop, you know, reporting and finding out ways to remediate issues from like a risk perspective and then making sure that it all falls in line, that we can kind of tell a clear and concise story to the street is kind of where I guess the comp-
compliance aspect would come in.
Raj Krishnamurthy (25:44.745)
And what role does, maybe it’s a cheesy question, but what role does automation and continuous controls monitoring play in that?
Evan Millman (25:54.677)
everything, right? Because like ultimately the hardest part about security is always going to be people, right? You just simply like machines are just faster, no more than all of us combined, right? And certainly AI is there is right at the forefront of that. Constantly being able to check on things, constantly being able to audit things.
I think that does two really important things. Like A, I think that instills really good behavior, right? Like I have a four year old at home. We never, like we, my wife and I, we’re not big on like baby proofing our house. Like we really never did that. But how did my, you know, son and now my daughter, how did they learn, like don’t touch the stove when it’s on.
Like don’t go down the steps is through when no one’s around is through repeated behavior of don’t touch that. Don’t touch that. Don’t touch that. Eventually like that gets ingrained. Like they’re not going to touch it anymore because they just know not to touch that. So like I think if you take that same kind of methodology and apply it to, you know, to businesses like, okay, don’t push code on unless it’s gone through this review. Don’t push code till it’s gone through this review.
Eventually people are gonna be like, if I do that, like Evan and his team is gonna find out eventually and slap me on the wrist again. So I’m just not going to do that. So it’s like through learned behavior, I think is really what kind of helps drive change, I guess if you will.
Raj Krishnamurthy (27:40.063)
And you see automation as the means to enforce that, bring about that change.
Evan Millman (27:43.843)
Yeah, so automation, I think, could help by, right? it’s, again, like I can’t always be observing, right? Like my team, you’re always gonna have limited human resources, right? So automated checks can really help and be that, like the tentacles from like my team that’s like out there observing in the wild, right? Like I’m not gonna have somebody who’s like constantly sitting in our prod environment, like.
checking code to make sure it’s compliant or making sure that every time everybody sends a sensitive document outside of our organization that they’re making sure it’s being encrypted, using an encrypted source. of course my team is never going to be able to check and observe everything, which is where things like automation really come into play because then you have like
machines or technology better that’s helping you to achieve that goal. That’s helping you to maybe put up a guard rail or preventing you from pushing code to production because you haven’t done X, Y, and Z, or it’s constantly monitoring, you know, an environment to see something, you know, to see some type of vulnerability. So the automation kind of really helps to be the
the eyes and ears and kind of stopgap where kind of human resources would lack.
Raj Krishnamurthy (29:22.483)
One thing we constantly hear is that this one size fits all automation does not fit anybody, right, to be honest. And because every company has their own contextual process, it is driven by their own threats, by their own risks, by their own, the environment that they are in. How do you see that? So to what extent do you have to tweak this automation to make it worse?
Evan Millman (29:48.249)
Yeah, 100%. Like never, no, no human being is the same, right? No organization is the same. There’s similarities, but nothing’s ever going to be completely black and white. Totally the same. So it’s, it’s very much like my, I guess I would answer that the same way as how I view, you know, like, like compliance standards where it’s just the foundation, right?
But then you have to mature certain controls to better fit your environment. like automation is the same way, right? It’s just the foundation. But then you have to fine tune those automated resources to ensure that they align with ultimately like your control set, with your security posture, with your policies and procedures, with your requirements from your customers, with your requirements from your
compliance needs that you have. To think that you can just take a tool and drop it into every organization because there’s some automated workflow that will prevent you from doing X, Y, and Z, it’s foolish, right? I would argue anybody making that statement has very little experience in the technology world, right? Like every…
organization does things a little bit differently and keeping that in mind and I think, you know, personalizing those type of controls to an environment is super important.
Raj Krishnamurthy (31:35.733)
So that means that it is a partnership between the GRC teams, the GRC and the other teams, and also the vendor, right, from a tool perspective.
Evan Millman (31:45.569)
Always, 100%. Yeah, they’re like, hate, and but, know, sometimes too much customization can also be a bad thing, right? Like there needs to be some standardization, right? But like a hundred percent, like when you’re certainly when you’re procuring like a security tool, it’s not
It’s not a one-size-fits-all. We had a customer on a call the other day and I forgot what the exact quote was but something along the lines of like that he want he like Security vendors should stop telling him what problems he needs to solve and just give him solutions, right? like all you know, if you’re coming out with some product or
You have some new tool that has some new level of automation or whatever, like, and you just blindly call an organization and think that like your tool is going to solve their problems. You’re just so naive to actually what happens, right? Like, and listen, I get it. I’m not in sales. So like, I know that sometimes like there is no other way, right? Like I get it. Like my friends who are in sales would argue with me that like,
Raj Krishnamurthy (32:57.697)
You
Evan Millman (33:04.664)
Hey, actually by the numbers, like you still can like receive some level of traction, some positive feedback by just cold calling people and just like telling them that they have a problem that like you can fix. Like I get it. But again, just like with everything, you got to take it with a grain of salt, right? So like, but really you don’t know if that tool or you know, or that product.
is right for that organization, is going to solve any of their problems, is not going to just be, you know, implemented and never used, you know, that’s the biggest thing that I hate when, you know, when we’re doing analysis, you know, from like a third party risk management perspective of what tools are we using? Like how many software tools do we buy that we never use because somebody on the sales end
Raj Krishnamurthy (33:59.35)
No use.
Evan Millman (34:02.478)
was on, know, took us to a Yankee game and, you know, promised us that, you know, this XYZ tool will do everything and solve all of our problems. Like, no. Like, the only ones who really know who can solve all your problems is yourself, right? Like, you have to be self-aware as an organization, as a mature organization, you should be self-aware of, like, what really are the challenges and what tools can help.
me fix those challenges and maybe there are tools and automation that can help with it and maybe there aren’t. But you know, always like a vendor should be working hand in hand. There should be a problem that needs to be solved in order to procure some new fancy tool, whether it’s written with AI or automation or not.
there should be a problem that you need to solve and that’s why you need to get something. Otherwise, like sometimes simple is better, right? Sometimes not having something and just going about it the way that you’re doing. Sometimes just using a boring old spreadsheet is just like, sometimes that just works for a certain organization, right? Like.
Raj Krishnamurthy (35:15.553)
Yeah
Evan Millman (35:23.106)
Like it’s just, it’s not a one size fits all thing. And you know, I get that that’s hard for software vendors to hear because they want to think that everybody is a prospective customer. But like, that’s just not honest. Like that’s just not real to me.
Raj Krishnamurthy (35:37.61)
to everybody their own. And this partnership requires investment, investment from you, investment from your teams, investment from other teams. How do you go build that business case with your leadership?
Evan Millman (35:53.603)
Yeah, it’s hard. again, I think, you know, I like to look at everything from a risk perspective and a business perspective, right? So like a mature organization will have a robust risk management program where you will constantly be assessing, reporting.
and analyzing risks to an organization. Like this is in my head how it should work, right? And then based off of those risks, the appropriate stakeholders would discuss what remediation actions are needed to combat those risks, to remediate those risks. Based off of that, then you might need to go out and procure a tool or enhance a policy or procedure.
And then because you went through that whole process of somebody reporting on a risk, talking about those risks with key stakeholders, everybody agreeing that, yes, that’s something that we need to fix. That kind of like alleviates some of the tension when you want to then go procure a new tool just out of nowhere where somebody’s like, well, why we have X, we have all of these like committed projects for the next three quarters, like
We don’t have time to do an evaluation. We don’t have time to do a business case because you kind of put the cart before the horse there, right? Like, so if you were operating more from like a, a risk governance perspective and you bake into your project planning and your, your workload for, you know, the next quarter or the quarter after that, that you need to remediate X, Y, and Z risk.
and we’re thinking about changing this procedure and we’re thinking about buying a product that does something like this, that will help drive that buy-in from the stakeholders that need to have buy-in to make that process go quicker.
Raj Krishnamurthy (38:07.251)
And I think most of us are becoming from cloud-first companies to AI-first companies. What is your view? And how does, particularly with respect to what you’re doing in GRC.
Evan Millman (38:19.65)
Yeah, you know, AI first, know, AI is awesome and exciting and scary at the same time, right? I was in a meeting recently where somebody, a very senior level person at the organization was basically like, you know, before having this meeting with me, you know, you should dump all of your questions into
chatbot and you should send that over to me and I will then have that chatbot analyze and answer those questions based off of my historic work essentially alluding to the fact that like his Chat GPT or clawed instance knows more about him and the work that his team is doing than he does himself so like when you think of it from that perspective like
It’s like mind blowing of like, wow, how amazing, you know, these AI tools can be, but like you can’t help but think of like, okay, well, what else does that chat bot know about you? Like where, where is, privacy considerations cons, you know, in there? what, what if your chat bot has, you know,
Access to highly confidential business IP You know that would obviously be a huge concern. I think you know we are In a stage right now where? Businesses and organizations AI like want to just jive into like AI and AI and all these cool things that AI can do and it is really cool and it complete it saves tons of time I I
tell my team all the time to be using these tools because it really does save time where tasks that used to take hours now can take minutes. But at what cost, right? I think that not enough is being done to consider and understand the cost, right? Like nothing’s free. like, I love like people, like,
Evan Millman (40:40.972)
my parents would like, you know, novel like how is like Gmail for free, right? It’s like, well, you don’t fundamentally understand if a tool is for free, that means that you’re the product. Google doesn’t just want to give you an email client for the hell of it, right? Like they’re not just giving it because they’re nice and like, and philanthropic, they’re giving it to you for a purpose, right? And it’s the same thing of
Raj Krishnamurthy (40:59.873)
You
Evan Millman (41:06.946)
when these AI tools are collecting all of this information about you. Yeah, that has a really cool use case that you can use and you can feel, but what are they doing with your data at the backend? Like those are the questions that I think we still have yet to answer.
Raj Krishnamurthy (41:24.481)
I think it sounds very dark but the way that I was running through my head is that they are not selling to you but they selling you is what you saying.
Evan Millman (41:34.095)
100 % I mean 100 % like it’s it’s scary right but like think about it like you know meta like they’re in the business of making money they don’t just care that you like share your photos with your friends and family like that’s not they’re not as you know as great as you want to like you know put these tech leaders on a pedestal like they’re they’re not trying to give away things for free
And it’s the same thing with AI, right? And listen, we do everything that we can internally to ensure that we are comfortable with the tools and technology that we use. We document risks, we evaluate risks, we make sure that there’s no shadow IT going on where teams are just procuring this tool or that tool. So we do…
practice what we preach, you know, what abnormal and we do try and mitigate, you know, those risks as much as possible. but it is certainly a question, right? Like it’s again, to me comes back to like business and risk decisions. Like there are some risky behaviors that organizations are always going to choose to do because it’s in the best interest of the organization, right? There’s, there’s multiple ways to treat a risk.
that’s identified and one of those is just accepting it and like that sometimes that is okay. but again, accepting a risk I think can only is only is a product, a mature organization accepts the risk when they have fully documented and fully evaluated a risk. And, ultimately decided that like going ahead and still using that tool, or still
procuring that product has a greater, the benefit to the business outweighs the risk. And so ultimately, like it’s all about making sure we document and observe and providing that information and making informed business decisions.
Raj Krishnamurthy (43:48.578)
And particularly on this topic of AI and the AI for security and the security for AI, how do you see the frameworks like ISO 27001, CSA recently has had this AI governance framework. What do you see as the role of these frameworks in the maturity of adoption?
Evan Millman (44:10.722)
Yeah, you know, so, you know, or like the new 40 ISO 4201 that came out about last year. Again, like I just like with all other compliance standards, I’ve I’ve it’s the same way, right? It’s the foundation. Those type of certifications or frameworks, they’re helping to build a framework where
more where you’re forcing engineering teams to monitor how code gets pushed to production, to have compensating controls, to do audits, to make sure that there’s no bias in your code, in your AI. So these frameworks help to build those basic building blocks. But
Just like with any other certification, I would argue that’s just the beginning, right? Like that should just be the table stakes. That should just be what gets you in the door. What makes you a more successful organization in terms of your risk management or your security posture is taking those and then elaborating on them. So taking the requirement from a framework and implementing that, but then going a step further and making sure that you
are doing more than just what is required. That is really, I think, the role in which these certifications play. Like, without them, I would argue probably we wouldn’t be doing a lot of anything, right? So, like, it’s the same thing, like, back to, like, the highway analogy. Like, if we had no speed limits, everybody, it would be the Autobahn, right? Like, everybody would just be going, like, a hundred miles an hour. I get to get to my friend’s house or to…
back to go visit my parents as quickly as humanly possible and I’m going to go as fast as I possibly can. But like there’s a lot of risk there, right? That’s not safe to put it quite frankly. And so I think what these frameworks are starting to do is to help to build the guardrails or to help to build the auditability of these AI development programs.
Evan Millman (46:33.17)
so that we can decrease risk, right? You’re never ever going to get to a place where there is no risk. People like me wouldn’t have a job if like we were ever in a place where there was no cyber risk. But we can get to a place where we can manage it and control it. And I think that’s where these kind of these frameworks help to build those foundation, foundational blocks.
Raj Krishnamurthy (47:00.065)
And if I were to paraphrase the Spider-Man quote, I think with increasing speed comes increasing responsibility. And traditionally, I think the GRC teams were left behind in terms of how models were developed, how models were deployed. I’m talking about the machine learning models, right? Do you think that is changing? Is there more
Evan Millman (47:07.566)
Exactly, absolutely.
Raj Krishnamurthy (47:29.855)
sort of responsibility or accountability with the GRC teams? Are there more things happening with the GRC teams right now than before?
Evan Millman (47:38.787)
I think we’re trying to. I fear though that like not enough. Just like the early days of the internet when you never really considered that, you know, I’m Evan Millman and I’m going to create a username or an email address that has nothing to do with my name or sign on to a social media platform and pretend to be you Raj, right? Like I can…
to get your picture from the internet, I could take your first name and last name and create an account and there’s nothing that is preventing me from doing that, right? They’re like access control and authentication and authorization was an afterthought at the beginning phases of the internet and now we’re left with what we have now, right? Which is where, I mean, what’s the latest statistic that like…
More than half the accounts on Twitter, on X, are all bots. You might think that you’re interacting with somebody who’s real, but you’re not. There’s really no way to properly govern that because authentication and authorization was just not built into how we think about what the internet is today. I fear that we’re doing similar with AI. I think…
Probably marginally better because I want to think that sometimes we learn from our past mistakes but it the speed in which some of these AI tools and like and You know models are being developed It’s it leaves question marks in my head of like are we actually? Repeating our you know mistakes of the past and just like the new
iteration for the current times or have we learned and I think the jury is still out there.
Raj Krishnamurthy (49:38.369)
And it’s a very, I think it’s an interesting world situation in the GRC world, right? On one hand, you’re dealing with machine learning data engineers, data scientists, machine learning developers, right? And large language model and large reasoning models are getting added to the mix. You’re dealing with cloud infrastructure engineers, platform engineers, DevOps teams that actually are operating at a rapid clip on tools like Kubernetes, right? Platforms like Kubernetes and cloud.
and then you’re dealing with all the security tools and the plethora of tools that are coming about. How much do the GRC teams need to be technical in order to deal with this stuff?
Evan Millman (50:15.928)
Hmm. Yeah, great question. I it’s a, it’s honestly a hard question to answer because I could argue it from both ends, right? Like I can argue it from the end of the GRC teams don’t really need to be technical because they are, you know, just
the referees, right? And they’re just trying to call balls and strikes, right? An NBA referee doesn’t need to know the technique behind shooting a free throw shot, right? Like they just don’t. But they need to know that like, your feet need to be behind the line, right? So like, GRC teams, you could argue, need to know the rules.
and so that we can observe and report about them. However, I could also argue that if you did know how to, more and more technical that you are, the more robust conversations you can have with these teams, right? So like the easier it is to let your, to have these teams like let their guard down and really bring you into the fold. The easier it is to,
earn respect. like, do they need to know? Is, you know, can they be effective in their jobs without being technical? No. But does a culture, a more dispersed culture of security, is that a product when GRC teams, when the people who are calling ball and strikes
actually know the pain points that these teams are delivering. Yeah, I’d argue it’s hard to argue against that, right? I mean, again, can we still be effective and do our jobs well? Yes, absolutely. But potentially there is a stronger partnership when you can talk about EC2 clusters and Kubernetes and all these
Evan Millman (52:38.926)
deep in the weeds technical topics when GRC teams can talk about them with engineering.
Raj Krishnamurthy (52:49.867)
No, sense. So the referee doesn’t have to be a league player, but they should at least know how to play ball.
Evan Millman (52:56.074)
Absolutely. like, and yeah, and like again, it’s not to say like it has to be that way, right? Like you can still be effective without being that way. It just might be harder, right? It just might, you might take you longer to win over certain teams to gain their respect, right? Like people, it’s a people, like I honestly say like that, that to me is a little bit more of a people problem, right? Like.
If I am the lead architect at an organization, I’m more prone to want to work with somebody that I respect, understands the pain points that I’m going through. It goes back to that, just because I’m in security doesn’t mean I can pout my chest and say, I know better than everybody else.
You actually don’t. And like there might be things and issues that pop up that you can’t anticipate because you don’t have the technical know-how, because you don’t know what they have to deal with in order to reach their business goals. So like, think having GRC teams being more technical or at least being able to talk the talk, right? You don’t have to walk the walk, but you definitely have to talk the talk.
helps build those personal connections with the engineering teams that will ultimately help them buy into your initiatives and the things that you’re trying to prove to get across the finish line and ultimately build that culture of security across the whole environment.
Raj Krishnamurthy (54:43.423)
And how do you think other teams view GRC, engineering security?
Evan Millman (54:50.854)
Yeah, so I’d say it’s a mixed bag. I’ve worked with engineers who very clearly, day and night, see GRC as a partner, as a necessary component in order to achieve a common business goal. Absolutely, whether that’s…
reporting on risk or driving in certain initiatives, you know, or making sure that we’re compliant with certain standards. You know, they see it as like a necessary partner and they’re a willing and able partner, just like how you were talking before about like, an engineer, like they’re just really concerned about, you know, getting their job done, pushing code out to production, like doing what they have to do.
And maybe they’re not thinking about all these security or compliance ramifications. Whereas like the GRC team is thinking about like, well, if we want to sign on this huge household name customer to our product, they’re requiring us to do A, B and C and engineering teams, you’re not doing that. So like, we’re going to observe and call out when you’re not so that we can point it out so that you can remediate that.
And we’re an engineer might just like not have the bandwidth or just not might not be thinking that way. like a hundred percent. However, also like we can be. You know, the, the, the one who’s imposing, you know, the, the, the speed limit, right? Like maybe they want to push out, for a very crude analogy, you know, like a million lines of code, you know, a day. And GRC comes in and says, Hey, you know, actually.
No, that’s too risky. Like we only can push out like a hundred thousand, know, thousand like lines of code of day. right away, like we’re going to be, we’re going to be the scapegoat. Like we’re going to be the, the, the, the roadblock in that’s preventing teams from achieving their goals. So it’s important. when those situations come up to really partner.
Evan Millman (57:09.858)
with engineering teams and it could not, it’s not just engineering teams, right? This could be legal, accounting, people ops. Like it’s not just, you know, I, like to remind people that like, know, GRC is not there just to monitor and, and, and, know, be a traffic cop for just, you know, IT and engineering, but it’s really across the whole organization. It’s honestly, one of the reasons that I love the GRC space so much is because like one day I’m talking to the chief architect, the next day I’m talking to the,
you know, chief, you know, our head general counsel, like the next day I’m talking to the head of like people ops, like literally, I mean, maybe only the CEO has that type of cross communication with across all departments as like the GRC team does. So it’s really important when GRC teams are kind of viewed as that roadblock that they build relationships. You know, I’m a big, big believer in like a lot of it is just like,
It’s the soft skills sometimes that matter so much in GRC It’s just connecting with people and like so again sometimes that’s easier because like I can Sit in your shoes and I know what you’re talking about when you’re talking to me about Kubernetes or EC2 instances or you know What what have you but it’s you know, it’s it’s building relationships and it’s making
Other teams or departments understand where you’re coming from and why you’re doing certain things. The why is so important in GRC. It’s not just because I said so. It’s not just because Evan knows more about security because Evan has his masters or his CISSP because I’m a security expert. Like, nobody cares about that. The why comes from Evan explaining like, hey, I know you’re super busy and I know
that this is going to put a load on your team and this might slow you guys down. But we’re really, we’re trying to sign this client and they need us to do X, Y, and Z and they need us to be compliant with this standard or they have their own internal standard that they need us to be compliant with. And we all are on the same team, right? Our mission, our goal is all one. And we’re just trying to help ensure that we achieve that goal together. So the why,
Evan Millman (59:34.38)
sometimes in GRC is so vitally important.
Raj Krishnamurthy (59:37.634)
That’s beautifully said. So I think what you’re basically saying is knowledge builds empathy, empathy builds relationships, relationships build conviction for everybody else to do the right thing. Beautiful. You, I think as we said earlier, as I said earlier, Evan, you actually have a very, very interesting journey, right? You started as a paralegal, went and worked as a network engineer. And then, you know, we did a consulting thing on security and then…
You are now the head of GRC, or leading the GRC program at ABNO.
What would you say to somebody who wants to be the next step and trying to follow your footsteps and you know from different walks of life trying to get into GRC, what would your advice be to them?
Evan Millman (01:00:18.574)
You
Evan Millman (01:00:24.494)
I mean, as a joke, would say, you know, maybe major in computer science or something more technical in undergrad to like have a foot up on engineers, you know, in the early stages, I would say.
You know, it don’t close the doors to any opportunities, right? So basically like long story short, my journey was, yeah, I was a political science major at undergrad and I wanted to go to law school. And I was advised, you know, not to go to law school right away out of college and to kind of work in the legal industry for a little bit. And seafood is really something that I liked. So I worked as a paralegal.
mostly like at real estate law firms. And I went and I sat for my LSATs and I had a good GPA and I had a good LSAT score. And there was just a gap between when like law school would start and like when I was done with my test. I was like, you know what? Like I wanna, I’m someone I love learning. Like my wife would joke that like if I could, if being a student could be a profession like
sign me up. Like I love going back to school and all that stuff. So I was like, all right, you know, let me sit for, let me see what else I’ve always been interested in technology. My parents would, my, my family would allude to like, I’ve always been, you know, you know, I want the first iPhone that comes out, the first this that comes out, like that, that’s just, you know, always kind of been in my nature. So like, I’ve always loved and, and, and had an admiration for technology. So in that gap, I was like, you know what, let me
I’ve never considered it. was like, let me go see if there’s like a course I can take. I know just like general in computers. And I signed up for a postgraduate program at a local college by my parents in in CIS. And I loved it. And it was like, I think, I think my GPA from that program was like exponentially higher than my already.
Evan Millman (01:02:39.084)
very respectable GPA from undergrad. And why was Because I was just like interested. Like I just like, it was cool. Like when I learned like C++ and I made, I coded a computer program that was like a calculator. I was like, this is so cool. Like I instantly like, learning becomes a lot easier when you’re actually interested in the material, right? So I, you know, I finished up that program and then I was like, you know what? Like,
Raj Krishnamurthy (01:02:53.739)
You
Evan Millman (01:03:05.868)
Why do I want to go to law school? Like the, the, the why, like a lot of it comes back to again, like the why, like what, what was the purpose? So I actually decided not to go to law school and I, did some networking and you know, how the story goes is, know, I was dating, you know, you know, my girlfriend at the time, now my wife, had a friend who had a friend who worked at a telecom company.
And like when I was going, you know, when I was in this program at CIS, you know, doing the CIS program, was like, telecom, like that seems so boring. Like who cares about like the telephone lines and like all that stuff in the street. Like, of course, like that’s me being a complete novice because like telecom is vitally important. And if you only, if everybody understood that ultimately everything is connected by a hard wire somewhere, some way, you know,
fiber lines down in the middle of the ocean. Like it gets really complicated and really cool and interesting. And so like I took a phone call and I instantly hit it off with this person. He’s actually still a good friend and mentor of mine. And it just kind of like opened the door to a career in technology. And that’s when I went and became a network engineer and, you know, and my mentor, he actually had a background in security. So he was the one who actually kind of pushed me.
Raj Krishnamurthy (01:04:22.804)
you
Evan Millman (01:04:32.75)
into the security realm once he saw me going for my network plus, my CCNA and like all that stuff and just kept on excelling and excelling and he was like, hey, like, you know, should try where like the industry is moving towards, you know, more security. So then, you know, I went and went for all my security certifications and security plus and CISSP and all that fun stuff. And so I guess I would, you know, and then ultimately I was, I was,
had the experience in technology and then a bit of the security background to then warrant a role that’s more directly in security. And so then I started my journey in security and then I fell into GRC because again, like from my background, I’m not super technical. Can I talk to our engineers, you like we were alluding to before? Sure.
Do you want me, you know behind like a command line during the day like probably not no not where my strong suit is but I that’s why I like GRC because I always felt it was like a good mix of That kind of like business soft skill Adaptation and also that technical knowledge. It was like a good mix for me
and then sprinkle in kind of like my experience in the legal industry. like GRC just kind of like was like, like the Venn diagram, the thing in the middle, just like always seemed to be GRC. Like could I have gone back and studied and become, know, pursued a more technical path? Absolutely. But like it just, it just fit in my personality and my experience. So I guess I would tell anybody who’s trying to be the next Evan Millman.
to keep trying, right? You never know what conversation, what door, where that’s gonna lead to. I remember when I was trying to get into the security space, I was meeting with anybody and everybody. I I remember meeting with like this partner from like PWC and this person from this consulting company and this one and like just using your network.
Evan Millman (01:06:55.37)
It’s sad, but like that’s the way of the world, right? Like sometimes it is who you know, and that’s not like in a bad way that like that’s going to leave people out, but just in like everybody knows people, right? Well, maybe it’s a professor that you worked with, like a college. Maybe it’s somebody that you work out with, like at the gym. Like I would say like for somebody who’s trying to start out, whether that’s like a career in technology or GRC or what have you, it’s like,
The more the broader reach your network can be, the more opportunity you can find. The easier it is for you to actually find a job and a career path that you will feel fulfilled in, that you will enjoy, that you will want to pursue. So, you know, my best advice would be, you know,
Never say no to a phone call, never say no to a coffee meetup, never say no to grabbing dinner, even if it’s awkward, even if you feel like you’re out over your skis, even if you feel like you’re not qualified, you just don’t know. You don’t know the path that you might be on. And I’m somebody who thoroughly believes everything happens for a reason and…
Raj Krishnamurthy (01:07:55.396)
Ahahaha!
Evan Millman (01:08:22.33)
You can’t get to where you’re going without hardship, without failure, without adversity, without figuring things out. Nothing is easy. There is no easy path. That’s a lie. I’m a firm believer in that. You have to figure things out yourself. And it’s not gonna be easy. It’s not gonna be carefree. But you have to put in the work and you have to try.
Raj Krishnamurthy (01:08:48.555)
That’s beautiful. That’s a fantastic story, Evan. I want to give you the last 60 seconds. Any shout out to books, mentors, anybody that you want to call out that has helped you get this
Evan Millman (01:09:05.386)
sure. mean, so I was just saying, a mentor of mine, he’s actually, one of the, CISOs right now at Robin Hood, David Schwed, very fascinating, person who was actually, when I met him, he was the general counsel and CIO of the telecom company I worked for. and he’s somebody that has, really helped me, in my career and my career path and just like been
like a great sounding board to this day. And, you know, I guess I’d also, you know, I give a shout out to, you know, my current team. You know, I work with a great group of individuals, whether those are the people who work on my team or even my supervisors, Liz and Mike, they’re just like being able to work with people that you trust, that you admire, that you respect.
that know more than you is just worth so much gold. And I’m so grateful for the position that I’m in right now and the opportunities that I have, everything going on at abnormal, just the industry that I’m in. It’s just every time I talk to somebody, they’re like, I was out last night with a couple guys from the neighborhood. went to a place to go play golf at night.
And instantly I was like, when I was talking to somebody new, was like, what do you do? was like, I’m in cybersecurity. They’re like, wow. Everybody’s like lights, their eyes light up. So just, I’m totally grateful for where I am and where my career path has led me. So definitely some shout outs there. Books, it’s funny because I remember,
you know, interviews, you know, throughout my career, there was always that question, okay, like what do you do to stay up with like industry trends? You know, and you know, I could rattle off, you know, cyber wired daily podcasts that I listened to once in a while, or like the Krebs on security emails that I get, you know, or, you know, the organizations that, you know, are involved in. But honestly, there’s so much information out there. If you just follow the right,
Evan Millman (01:11:26.624)
organizations on Twitter, on LinkedIn, I mean, there’s just like, you don’t even need to have like one source anymore. It’s just like, there’s so much out there that if you just stop and listen, it’s just all right in front of everybody. So like, yeah, I can’t emphasize enough how much tools like LinkedIn or social media also play a part in just keeping.
Myself and I think most people these days up with like the latest trends in the IT world
Raj Krishnamurthy (01:12:00.435)
Evan, this was a fascinating conversation, and thanks for being on the
Evan Millman (01:12:05.144)
Thanks for having me, Rob, really appreciate it.
Listen on your favorite platform and stay updated with the latest insights, stories, and interviews.
Want to see how we can help your team or project?
Book a Demo

