How CISOs are Modernizing GRC: 10 GRC Challenges Solved by Continuous Control Validation
CISOs responsible for GRC teams tend to describe the same operational friction.
- Evidence collection is manual.
- Control status differs between production systems and the GRC platform
- The same access control is tested separately for SOC 2, ISO 27001, and NIST.
Whether the platform is ServiceNow IRM, Archer, AuditBoard, or LogicGate, the pattern is consistent.
- These systems are governance and workflow platforms.
- They orchestrate risk registers, control documentation, attestations, issue management, and audit reporting.
They are not designed to continuously validate live control behavior inside hybrid infrastructure.
Hybrid environments, like cloud, on-prem systems, Kubernetes clusters, SaaS applications, and custom tooling, all change daily. Configuration drift, tool inconsistency across business units, and AI-accelerated release cycles increase control complexity.
When validation does not keep pace with operational change, GRC becomes reactive.
The ten breakdowns below reflect this gap between governance orchestration and runtime control validation, and how introducing continuous validation reduces duplicate testing, manual evidence collection, and framework misalignment.
What is Continuous Control Validation?
Continuous control validation is the runtime evaluation of how security and compliance controls behave inside live operational systems. Rather than relying on periodic attestations, screenshots, or tool-reported status, it applies centrally governed validation logic directly to cloud accounts, Kubernetes clusters, on-prem systems, SaaS platforms, and custom applications.
The resulting control outcomes are delivered into the GRC platform in a framework-aligned format, allowing governance workflows to operate on continuously refreshed, operationally verified signals instead of static documentation.
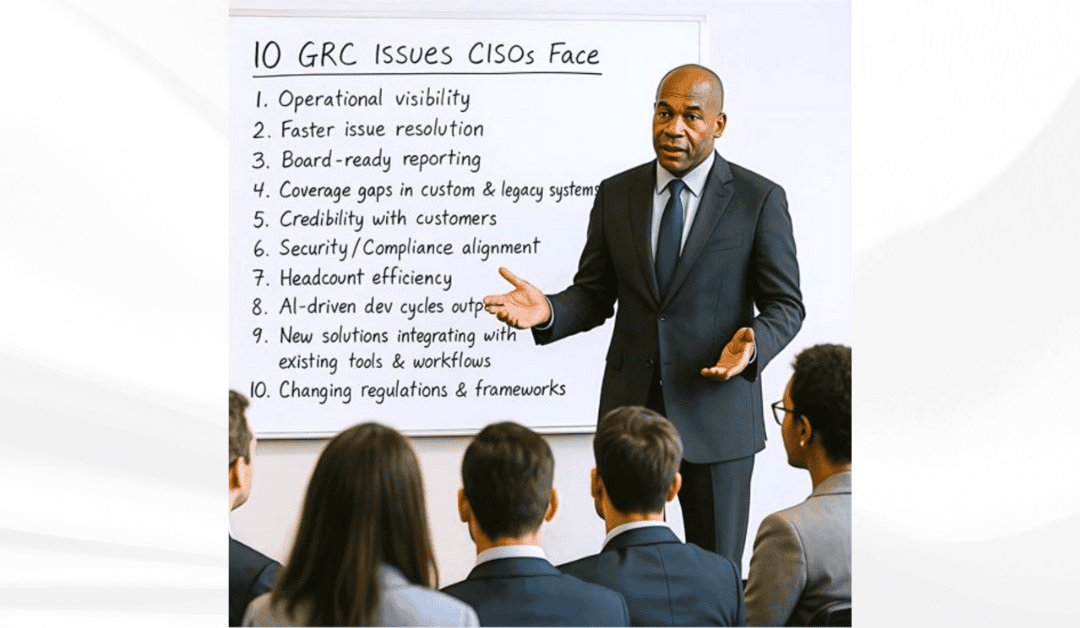
10 GRC Issues CISOs Face and How Continuous Control Validation Delivers Continuous Assurance
Most CISOs didn’t sign up to be compliance managers.
But as security and regulatory pressure has grown, more of their time – and their teams’ time – is pulled into GRC overhead:
- Evidence hunts
- Control gaps
- Framework mapping Framework mapping across SOC 2, ISO 27001, NIST, PCI
- Tooling misalignment across business units
These patterns show up consistently in conversations with GRC leaders on the Security & GRC Decoded podcast.
Below are ten recurring breakdowns, and how introducing continuous control validation reduces friction, duplicate testing, and manual evidence work.
1. Operational visibility
Problem: CISOs don’t know which controls are working until the audit flags one that isn’t.
ComplianceCow: Continuously evaluates live control behavior inside operational systems.
- Cloud accounts
- Kubernetes clusters
- On-prem infrastructure
- Custom applications
ComplianceCow feeds verified control results into the GRC platform. Drift is detected at runtime, not discovered during audit preparation
2. Faster issue resolution
Problem: CISOs’ teams get stuck chasing evidence and status updates instead of fixing real issues.
ComplianceCow: Collects and updates control evidence automatically, consolidates results by control objective, and synchronizes status with ServiceNow, Archer, AuditBoard, or other GRC workflows. Teams move directly to remediation instead of spending cycles validating screenshots and chasing owners. Cleaner operational signals improve the accuracy of issue and risk workflows inside the GRC platform.
3. Board-ready reporting
Problem: Leadership wants answers CISOs can’t give without spinning up another data chase.
ComplianceCow: Validates control behavior inside operational systems, then connects those validated outcomes to enterprise risk, policy, and framework requirements inside ServiceNow, Archer, AuditBoard, or other GRC systems. This means that GRC dashboards reflect runtime control performance, not just documented intent, reducing last-minute data assembly before board meetings.
4. Coverage gaps in custom & legacy systems
Problem: Custom apps, on-prem, and legacy systems force teams into manual chases for screenshots, exports, and tribal knowledge.
ComplianceCow: Applies consistent control validation logic across heterogeneous environments, including custom applications, on-prem systems, legacy infrastructure, and ephemeral cloud workloads such as auto-scaling VMs and Kubernetes pods. Evidence is collected from live systems and synchronized with the GRC workflow, replacing screenshots and one-off scripts with governed, repeatable validation.
5. Credibility with customers
Problem: Security questionnaires turn into week-long scrambles. Miss one SLA, and confidence erodes.
ComplianceCow: Delivers continuously validated, security-framework-aligned control evidence into the GRC system, so questionnaire responses are backed by current operational data rather than last-minute screenshots. Teams respond with verified control status mapped to SOC 2, ISO 27001, NIST, PCI, or other applicable requirements, reducing scramble and strengthening customer trust.
6. Security/Compliance alignment
Problem: Security is focused on risk reduction. Compliance is focused on satisfying documented requirements. The two teams often operate on different data.
ComplianceCow: Produces validated control results based on live system behavior and links those results to both risk objectives and framework requirements inside the GRC platform. Security sees whether controls are functioning. Compliance sees how those controls satisfy SOC 2, ISO 27001, NIST, or other obligations and using the same underlying signal.
7. Headcount efficiency
Problem: Every new framework or major customer adds incremental control testing, documentation, and evidence collection. GRC headcount does not scale at the same pace.
ComplianceCow: Validates controls once in the operational environment and delivers those validated outcomes into the GRC platform in a framework-aligned format. Governance workflows can then apply that single validated result across SOC 2, ISO 27001, NIST, PCI, or other overlapping requirements, reducing duplicate testing and limiting headcount growth.
8. AI-driven dev cycles outpacing compliance
Problem: AI-assisted development increases release velocity and expands the code and infrastructure surface area. Manual or periodic compliance checks cannot keep pace.
ComplianceCow: Continuously validates control behavior as environments change, including cloud workloads, containers, and CI/CD pipelines. ComplianceCow then feeds current control behavior results into the GRC platform. In this way, assurance cadence now aligns with deployment cadence, and compliance does not become a bottleneck to engineering velocity.
9. New solutions integrating with existing tools & workflows
Problem: Many compliance initiatives require new workflows, custom connectors, and long rollout cycles, disrupting engineering and eroding goodwill.
ComplianceCow: Integrates with existing pipelines, ITSM systems, ticketing platforms, source control, and GRC tools, validating controls within current operational workflows and delivering results into the governance layer. Teams do not have to redesign how they work in order to maintain compliance.
10. New regulatory obligations entering scope
Problem: New regulatory or customer-driven framework requirements enter scope under deadline pressure, impacting audit readiness and executive confidence.
ComplianceCow: Applies consistent, centrally governed control validation logic across operational systems and delivers those validated, framework-aligned results into the GRC platform. The GRC system remains the system of record for risk registers, policy documentation, issue management, and reporting, but now operating on continuously refreshed control outcomes derived from live infrastructure rather than static attestations. When new standards enter scope, governance teams update mappings inside the GRC system rather than re-running validation across infrastructure.
Conclusion: Why GRC Platforms Need a Continuous Control Validation Layer
GRC platforms such as ServiceNow IRM, Archer, AuditBoard, and LogicGate are designed to orchestrate enterprise governance. They manage risk registers, control documentation, issue workflows, attestations, ownership, and reporting.
Operational systems operate at a different layer.
Cloud infrastructure, Kubernetes clusters, CI/CD pipelines, on-prem environments, and custom applications change continuously. Validating how controls behave in those environments requires runtime evaluation, not periodic attestation.
When operational validation does not keep pace with infrastructure change, governance workflows rely on incomplete or outdated signals. Teams compensate with spreadsheets, scripts, screenshots, and manual follow-ups. Audit readiness becomes event-driven rather than continuous.
Modern GRC requires separation of concerns.
A governance orchestration layer manages policy, risk, issues, ownership, and reporting.
A control validation layer evaluates how controls function across live operational systems.
ComplianceCow operates in that validation layer.
ComplianceCow as the Control Validation Layer
ComplianceCow applies centrally governed control logic across heterogeneous environments and delivers validated, framework-aligned results into the GRC system of record. The GRC platform continues to govern risk, policy, remediation workflows, ownership, and reporting, now informed by continuously refreshed control outcomes derived from live infrastructure rather than static attestations.
This architectural separation changes outcomes:
- Operational drift is surfaced earlier.
- Remediation cycles shorten because evidence is current.
- Board reporting reflects validated control performance.
- Customer questionnaires draw from continuously refreshed, framework-aligned results.
- New regulatory obligations can enter scope without restarting validation across infrastructure.
ComplianceCow does not replace your GRC platform.
It strengthens the signals flowing into it.
For CISOs, GRC leaders, and platform architects, this means governance workflows reflect operational reality. Audit readiness becomes continuous. Security and compliance operate from the same validated control signal.
If this model reflects the challenges in your environment, a focused discussion may be worthwhile.
🔹 Book a demo to explore how a continuous control validation layer integrates with your existing GRC platform.
🔹 Listen to additional conversations with security and GRC leaders on Security & GRC Decoded.